Media Summary: What does the padlock icon on your internet browser mean and why is In this easy to understand video, we break down what The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ...
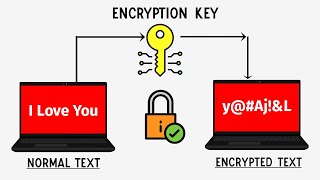
How Encryption Keys Work With Chris Bishop - Detailed Analysis & Overview
What does the padlock icon on your internet browser mean and why is In this easy to understand video, we break down what The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... This clip from the 2008 Royal Institution Christmas Lectures shows a simple demonstration of how two people can agree on a ... Make sure you're interview-ready with Exponent's system design interview prep course: In this video, we ... Sign up for a free Jotform account at: When safeguarding your company's sensitive ...
Learn more about Microsoft Research's Frontiers in Machine Learning 2020 event: ...