Media Summary: In this easy to understand video, we break down what Mia Epner, who works on security for a US national intelligence agency, explains how The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ...
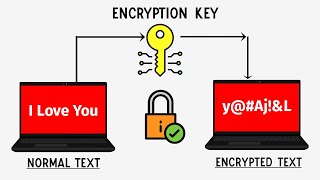
How Does Encryption Actually Work What Is An Encryption Key - Detailed Analysis & Overview
In this easy to understand video, we break down what Mia Epner, who works on security for a US national intelligence agency, explains how The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... SSH (Secure Shell) is the gold standard for securely accessing and managing remote servers. In this video, we'll break down how ... Sign up for a free Jotform account at: When safeguarding your company's sensitive ... Namaskaar Dosto, is video mein maine aapko
Make sure you're interview-ready with Exponent's system design interview prep course: In this video, we ... The most secure way to message someone privately is with a platform offering end-to-end