Media Summary: The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... In this easy to understand video, we break down what WhatsApp, iMessage, Android Messages and Signal all use the super-secure system called end-to-end
How Encryption Works And How It Can Be Bypassed - Detailed Analysis & Overview
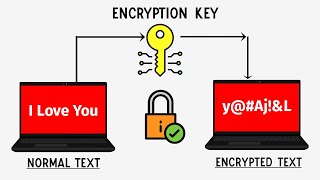
The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... In this easy to understand video, we break down what WhatsApp, iMessage, Android Messages and Signal all use the super-secure system called end-to-end Make sure you're interview-ready with Exponent's system design interview prep course: In this video, we ... How does data travel around the internet without becoming publicly visible? Start protecting yourself on the web at or use code SCISHOW to save 75% off of a 3-year Virtual ...
The most secure way to message someone privately