Media Summary: The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... Want to uncover the latest insights on ransomware, dark web threats, and AI risks? Read the 2024 Threat Intelligence Index ... V I D E O S T O W A T C H N E X T : Credit Card Counterfeiter: I Scammed ...
What Is Encryption And How Hackers Bypass It - Detailed Analysis & Overview
The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... Want to uncover the latest insights on ransomware, dark web threats, and AI risks? Read the 2024 Threat Intelligence Index ... V I D E O S T O W A T C H N E X T : Credit Card Counterfeiter: I Scammed ... A solid state quantum processor using qubits, is this the most powerful computer capable of actually breaking RSA In this video, we dive into the world of firewalls and uncover how they protect networks from cyber threats—and how Still using SMS text codes for 2-Step Verification? You might be at risk. In this video, I break down exactly why
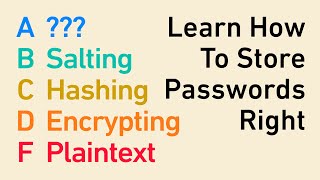
Most organizations believe enabling MFA is enough to protect their accounts. It's not. In this video, I break down how attackers ... In this video we will use a hardware attack to Thank you to ThreatLocker for sponsoring my trip to ZTW26 and also for sponsoring this video. To start your free trial with ... Have you ever pressed the Shift key five times on Windows and seen the Sticky Keys popup? What looks like a harmless ... If you're building an app or product, you _need_ to store your users' passwords securely. There's terrible ways to do it, like storing ... Two-factor authentication is one of the best things you can implement on your online accounts to keep them secure. But