Media Summary: How is your data protected when you browse the internet or send messages? In this video, we break down The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... In this easy to understand video, we break down what
How Encryption Works Explained In 1 Minute - Detailed Analysis & Overview
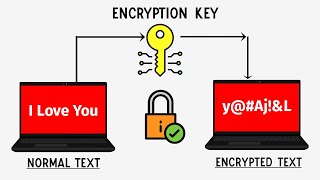
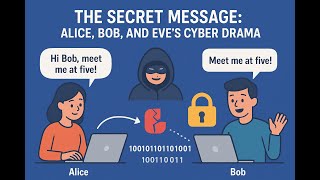
How is your data protected when you browse the internet or send messages? In this video, we break down The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... In this easy to understand video, we break down what Video walkthrough of code implementation: By the end of this video, you'll have a solid understanding of how RSA When messages are sent and received with end-to-end











![What is AES 256 bit-encryption? In 2 mins [ Simplest explanation of AES 256- bit encryption ]](https://i.ytimg.com/vi/AOgvutSpy3o/mqdefault.jpg)