Media Summary: Sign up for a free Jotform account at: When safeguarding your company's sensitive ... Mia Epner, who works on security for a US national intelligence agency, explains how DB2 Field Procedures (FieldProcs) were introduced in IBM i 7.1 and have greatly
Encryption Key Management Simplified - Detailed Analysis & Overview
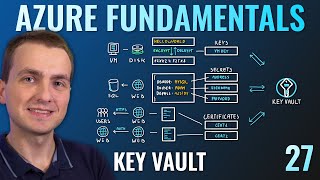
Sign up for a free Jotform account at: When safeguarding your company's sensitive ... Mia Epner, who works on security for a US national intelligence agency, explains how DB2 Field Procedures (FieldProcs) were introduced in IBM i 7.1 and have greatly I have seen a few questions on microsoft's mta about Enjoyed the video? Help me brew up more cloud content: ☕️ In this lesson, I describe methods of protecting and safely using private and symmetric
Interview with Josh Sousa of Torus, who is the VP of Sales for Western North America. Torus is a leading global provider of smart ... Securing sensitive information for our applications in Azure is very easy with Azure Ever wondered what secures your most sensitive digital information? This video demystifies the If you want to learn more check our AWS courses: ...