Media Summary: Sign up for a free Jotform account at: When safeguarding your company's sensitive ... Mia Epner, who works on security for a US national intelligence agency, explains how I have seen a few questions on microsoft's mta about
Encryption Key Management Explained Simply - Detailed Analysis & Overview
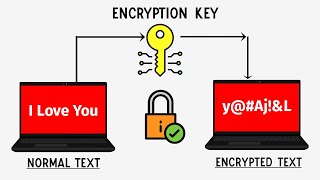
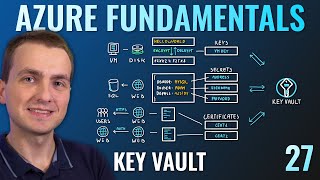
Sign up for a free Jotform account at: When safeguarding your company's sensitive ... Mia Epner, who works on security for a US national intelligence agency, explains how I have seen a few questions on microsoft's mta about In this lesson, I describe methods of protecting and safely using private and symmetric IITK - Professional Certificate Program in Blockchain (India Only) ... Securing sensitive information for our applications in Azure is very
Key Management in Data Security Explained 📺 Data Security Full Playlist : ...