Media Summary: The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... We use forms of Encryption everyday, but have you ever wondered what it is? Or How hard is it to find a 256-bit hash just by guessing and checking? Help fund future projects: ...
How Encryption Works - Detailed Analysis & Overview
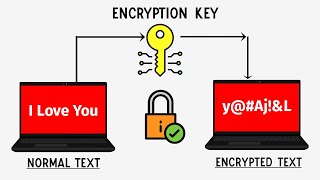
The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... We use forms of Encryption everyday, but have you ever wondered what it is? Or How hard is it to find a 256-bit hash just by guessing and checking? Help fund future projects: ... In 1997, a contest began to develop a new WhatsApp, iMessage, Android Messages and Signal all use the super-secure system called end-to-end In this easy to understand video, we break down what
Spies used to meet in the park to exchange code words, now things have moved on - Robert Miles explains the principle of ... One Encryption Standard to Rule Them All! : Almost All Web How do instant message apps do end to end Hey everyone, In this video, We'll understand how SSL certificates A quantum computer in the next decade could crack the