Media Summary: This video tutorial has been taken from Web Security. You can learn more and buy the full video course here ... Making yourself the all-powerful "Root" super-user on a computer using a Hello Everyone. In this video I am going to tell you about
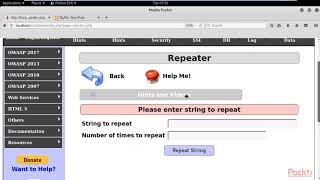
Owasp Buffer Overflow - Detailed Analysis & Overview
This video tutorial has been taken from Web Security. You can learn more and buy the full video course here ... Making yourself the all-powerful "Root" super-user on a computer using a Hello Everyone. In this video I am going to tell you about Date and time: - 19th July 2020 , 3PM to 5PM IST - Speaker: - Shibin B Shaji, Security Engineer UST Global, - Mohammed Shine, ... We updated this video for accuracy and improved graphics. Please view the new version here: Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔
1. Injection 2. Broken Authentication 3. Sensitive Data Exposure 4. XML External Entities 5. Broken Access Control 6. Security ...