Media Summary: This lecture is part of my undergraduate security course at the University of Cambridge. 00:00 Challenges and Making yourself the all-powerful "Root" super-user on a computer using a Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture discusses techniques for preventing
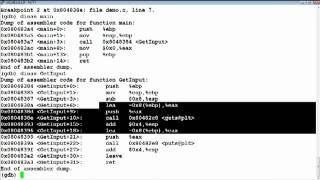
Owasp Melbourne Introduction To Buffer Overflows Stack Smashing - Detailed Analysis & Overview
This lecture is part of my undergraduate security course at the University of Cambridge. 00:00 Challenges and Making yourself the all-powerful "Root" super-user on a computer using a Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture discusses techniques for preventing This video is part of the computer/information/cyber security and ethical hacking lecture series; by Z. Cliffe Schreuders at Leeds ... Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture explores Disclaimer: The information presented in this video is for educational purposes only. It is not intended to be used for illegal or ...
HackRich In this Video I talked about what are the protection against a Computer Security Buffer Overflow Stack Smashing Detection Course Title : Computer Systems Security Course Instructor : Prof Vinod Ganapathy, IISc Pre-requisites – Standard undergraduate ... Hi everyone! I hope you enjoyed this video. Please do consider subscribing so we can continue making awesome hacking ...