Media Summary: 48. Buffer Overflow Attack on a Web Application This video tutorial has been taken from Binary Exploits with Python. You can learn more and buy the full video course here ... Team 6 (Jonathan Ojeda / Santiago Cabrieles)
Web Security Buffer Overflow Vulnerability Detection Packtpub Com - Detailed Analysis & Overview
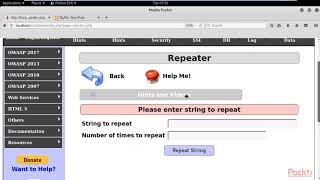
48. Buffer Overflow Attack on a Web Application This video tutorial has been taken from Binary Exploits with Python. You can learn more and buy the full video course here ... Team 6 (Jonathan Ojeda / Santiago Cabrieles) In this video, we present our project **" Making yourself the all-powerful "Root" super-user on a computer using a 48 Buffer Overflow Attack on a Web Application
I do not own any of company mentioned nor do I own any music inside of my video this video is made for educational purposes I ... This video tutorial has been taken from Metasploit Penetration Testing Recipes. You can learn more and buy the full video course ... Hello Everyone. In this video I am going to tell you about