Media Summary: In this video, we present our project **" Buffer Overflow Attack, DNS Poisoning Attack This video tutorial has been taken from Web
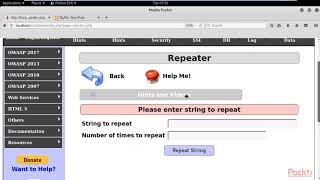
Security Vulnerability Detection Framework Buffer Overflow Backdoor Cache Poisoning - Detailed Analysis & Overview
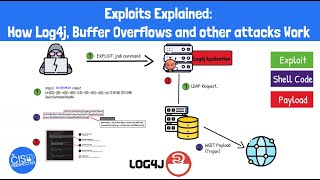
In this video, we present our project **" Buffer Overflow Attack, DNS Poisoning Attack This video tutorial has been taken from Web Making yourself the all-powerful "Root" super-user on a computer using a Hello Everyone. In this video I am going to tell you about Exploits represent any piece of code, data or sequence of commands that targets a
We updated this video for accuracy and improved graphics. Please view the new version here: I do not own any of company mentioned nor do I own any music inside of my video this video is made for educational purposes I ... This tutorial goes over the basic technique of how to exploit a In-depth solution to PortSwigger's "Combining web