Media Summary: If you would like to support me, please like, comment & subscribe, and check me out on Patreon: ... Making yourself the all-powerful "Root" super-user on a computer using a I do not own any of company mentioned nor do I own any music inside of my video this video is made for educational purposes I ...
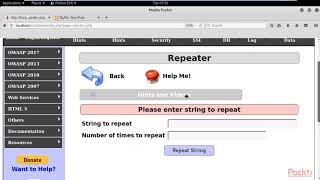
Penetration Testing Buffer Overflow - Detailed Analysis & Overview
If you would like to support me, please like, comment & subscribe, and check me out on Patreon: ... Making yourself the all-powerful "Root" super-user on a computer using a I do not own any of company mentioned nor do I own any music inside of my video this video is made for educational purposes I ... You NEED to know these TOP 10 CYBER SECURITY INTERVIEW QUESTIONS httpselevatecybersecurity.netinterview Get my ... Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ You NEED to know these TOP 10 CYBER SECURITY INTERVIEW QUESTIONS
This video tutorial has been taken from Web Security. You can learn more and buy the full video course here ...