Media Summary: Making yourself the all-powerful "Root" super-user on a computer using a This tutorial goes over the basic technique of how to exploit a You NEED to know these TOP 10 CYBER SECURITY INTERVIEW QUESTIONS httpselevatecybersecurity.netinterview Get my ...
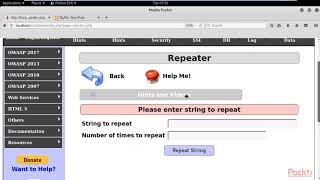
Real World Penetration Testing Buffer Overflows - Detailed Analysis & Overview
Making yourself the all-powerful "Root" super-user on a computer using a This tutorial goes over the basic technique of how to exploit a You NEED to know these TOP 10 CYBER SECURITY INTERVIEW QUESTIONS httpselevatecybersecurity.netinterview Get my ... If you would like to support me, please like, comment & subscribe, and check me out on Patreon: ... This video tutorial has been taken from Web Security. You can learn more and buy the full video course here ... We have a look at stack level 0 from exploit-exercises.com/Protostar and compile it on a current Ubuntu, to see if it's still ...
ethicalhacking Hello everyone. This video is a crucial part of my A short video explaining the security vulnerability stack-based