Media Summary: In this Week 12 assignment, we walk through a real-world style Making yourself the all-powerful "Root" super-user on a computer using a Security+ Training Course Index: Professor Messer's Course Notes: ...
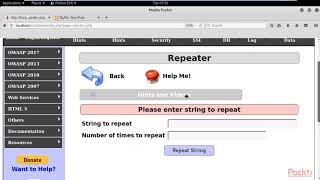
Owasp 5 Buffer Overflow Env - Detailed Analysis & Overview
In this Week 12 assignment, we walk through a real-world style Making yourself the all-powerful "Root" super-user on a computer using a Security+ Training Course Index: Professor Messer's Course Notes: ... Date and time: - 19th July 2020 , 3PM to 5PM IST - Speaker: - Shibin B Shaji, Security Engineer UST Global, - Mohammed Shine, ... This video tutorial has been taken from Web Security. You can learn more and buy the full video course here ... We updated this video for accuracy and improved graphics. Please view the new version here:















![Software Security [Fall 2023 W4 - Buffer Overflow]](https://i.ytimg.com/vi/72pmfO0WYNc/mqdefault.jpg)
