Media Summary: Solving format1 from exploit-exercises.com with a simple In this video I have discussed what format strings are, how they are used, and what are Hi there! This video introduces the core ideas behind
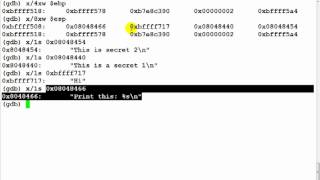
Format String Vulnerability Part 2 - Detailed Analysis & Overview
Solving format1 from exploit-exercises.com with a simple In this video I have discussed what format strings are, how they are used, and what are Hi there! This video introduces the core ideas behind This level turns out to be fairly easy when compiled on a modern Ubuntu. Finally :D format2: ... Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ Notes: - At one point I mention that there's a benefit to us writing the program with a fgets() rather than reading from argv, so that ...
FORMAT STRING VULNERABILITIES 22VV1A1232 CNS ASSIGNMENT Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture introduces









![[Fuzzy Security] - Format String Exploitation - Part 2](https://i.ytimg.com/vi/CHrs30g-3O0/mqdefault.jpg)

![ASE[2] - The Format String Vulnerability](https://i.ytimg.com/vi/Du3fVc_ZLiI/mqdefault.jpg)






![[02/03/22] SIGPwny Format String Attacks (printf) Meeting Recording](https://i.ytimg.com/vi/wfnd-dhSDr4/mqdefault.jpg)