Media Summary: Yeah that that's exactly the part why so sometimes the In this video I have discussed what format strings are, how they are used, and what are Okay it is recording good so today we are going to discuss
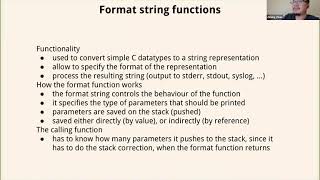
Cse 610 W10 Format String Vulnerability 2 - Detailed Analysis & Overview
Yeah that that's exactly the part why so sometimes the In this video I have discussed what format strings are, how they are used, and what are Okay it is recording good so today we are going to discuss Hello hackers today we're going to be talking about format strings and Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ VECTOR: Where Systems Collapse A 4-Week WEB HACKING Course by Cyber Secured India & VULNSHIELDS in collaboration ...
Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture introduces All right so now we know how to do an arbitrary read using Solving format1 from exploit-exercises.com with a simple [NEU CY 5770 Spring 2026] Week-10 Format string vulnerability Broadcasted live on Twitch -- Watch live at Notes: - At one point I mention that there's a benefit to us writing the program with a fgets() rather than reading from argv, so that ...



![Format string vulnerability [Software Security - Fall 2022 - Week10]](https://i.ytimg.com/vi/AN8MiXPmbqA/mqdefault.jpg)







![[NEU CY 5770 Spring 2026] Week-10 Format string vulnerability](https://i.ytimg.com/vi/I3pih8f-a6E/mqdefault.jpg)



![ASE[2] - The Format String Vulnerability](https://i.ytimg.com/vi/Du3fVc_ZLiI/mqdefault.jpg)
