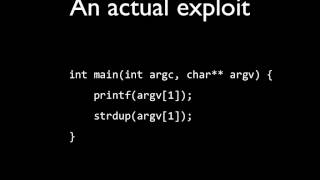
Media Summary: Format string vulnerabilities in ARM 2372626 In today's video, we explore the fascinating world of All right so now we know how to do an arbitrary read using
21 Format String Vulnerabilities Information Security 5 Secure Systems Engineering - Detailed Analysis & Overview
Format string vulnerabilities in ARM 2372626 In today's video, we explore the fascinating world of All right so now we know how to do an arbitrary read using A college course in Exploit Development More info: