Media Summary: In this video I have discussed what format strings are, how they are used, and what are Solving format1 from exploit-exercises.com with a simple Hi there! This video introduces the core ideas behind
Format String Vulnerability 23vv5a1269 - Detailed Analysis & Overview
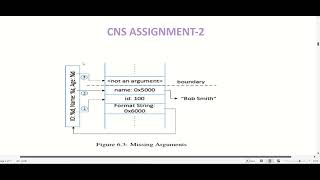
In this video I have discussed what format strings are, how they are used, and what are Solving format1 from exploit-exercises.com with a simple Hi there! This video introduces the core ideas behind Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ FORMAT STRING VULNERABILITIES 22VV1A1232 CNS ASSIGNMENT HackRich File Used:- In this video I have discussed ...
This video will demonstrate how to exploit a Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture introduces Sven Morgenroth is the Security Researcher at Netsparker. Sven joins us again to talk about 7th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. In this video we'll look ... TryHackMe room: Merch: ==== Social Media ==== Discord: ... Video walkthrough for "Floor Mat Store", a binary exploitation challenge I made for the 1337UP LIVE CTF 2023. It was a ...
pico ctf stack cache pwn challenge writeup,














![Format String Vulnerability - "Floor Mat Store" [INTIGRITI 1337UP LIVE CTF 2023]](https://i.ytimg.com/vi/Zu32BHwH-sA/mqdefault.jpg)