Media Summary: In this video walk-through, we covered another example of a vulnerable In this video walk-through, we covered a scenario of If you would like to support me, please like, comment & subscribe, and check me out on Patreon: ...
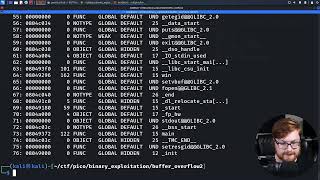
Buffer Overflow Binary Exploitation With Radare2 P21 Ctf Walkthrough - Detailed Analysis & Overview
In this video walk-through, we covered another example of a vulnerable In this video walk-through, we covered a scenario of If you would like to support me, please like, comment & subscribe, and check me out on Patreon: ... Our first video. In upcoming videos I will give voice don't forget to subscribe # This lecture is part of my undergraduate security course at the University of Cambridge. 00:00 Challenges and intro 01:40 What is ... In this video walk-through, we covered a guided example of
In this video walk-through, we covered another scenario of Correction: The program exits with status 1 and not 0 as it can be seen in the debugger but I mistakenly said it 0. This is the part 2 ... In this video walk-through, we covered another case of a PS, jump into the HackTheBox Cyber Apocalypse


![BASIC Buffer Overflow | Ryan's CTF [13] Everyday I'm Bufferin](https://i.ytimg.com/vi/YVlTDPhTA9U/mqdefault.jpg)