Media Summary: This tutorial goes over the basic technique of how to I delivered this session at SegFault community and many people requested me to upload the video. I have broken down the whole ... Making yourself the all-powerful "Root" super-user
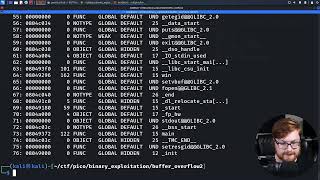
Buffer Overflow Under Linux Part 2 Practical Buffer Overflow Exploitation - Detailed Analysis & Overview
This tutorial goes over the basic technique of how to I delivered this session at SegFault community and many people requested me to upload the video. I have broken down the whole ... Making yourself the all-powerful "Root" super-user Buffer Overflow Attack using Heap - Demo - part 2 PS, jump into the HackTheBox Cyber Apocalypse CTF! Help the channel grow