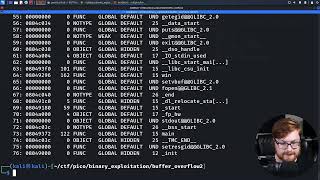
Media Summary: In this video walk-through, we covered another scenario of exploiting a binary vulnerable to When there is no 'system()' in program to use to drop shell. $ checksec ... In this video walk-through, we covered another example of a vulnerable binary to
Buffer Overflow Explained P22 Rop Chains Ctf Walkthrough - Detailed Analysis & Overview
In this video walk-through, we covered another scenario of exploiting a binary vulnerable to When there is no 'system()' in program to use to drop shell. $ checksec ... In this video walk-through, we covered another example of a vulnerable binary to In this video walk-through, we covered another case of a binary vulnerable to Receive Cyber Security Field Notes and Special Training Videos ... In this video walk-through, we covered a guided example of exploiting a vulnerable application to
That's the English version about this topic where I manually adjust the gadgets into the memory in order to execute VirtualAlloc ... encryptcvs 2019 all pwn challenges Stack Buffer overflow ROP ret2libc PS, jump into the HackTheBox Cyber Apocalypse