Media Summary: Hi guys my name is Alex and I'm going to give a brief introduction to Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ To help support me, check out Kite! Kite is a coding assistant that helps you faster, on any IDE offer smart completions and ...
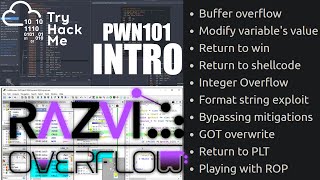
Exploiting Return Oriented Programming Rop Tutorial Binary Exploitation Pwn101 - Detailed Analysis & Overview
Hi guys my name is Alex and I'm going to give a brief introduction to Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ To help support me, check out Kite! Kite is a coding assistant that helps you faster, on any IDE offer smart completions and ... Let's learn some historical context behind The Intel vPro® platform helps mitigate low-level Let's learn about some specific techniques for
In this video we will see what a buffer overflow is, why does it happen and how to CTF Writeup Video 00:00 Intro 00:46 Running the When modern security protections like Data Execution Prevention (DEP) or the NX bit stop you from executing shellcode on the ...