Media Summary: To help support me, check out Kite! Kite is a coding assistant that helps you faster, on any IDE offer smart completions and ... Our most complex topic yet - how to do ROPs with Okay so we're today we're going to cover return oriented programming for
Pwntools Rop Binary Exploitation Downunderctf - Detailed Analysis & Overview
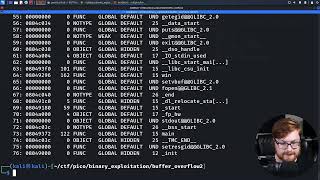
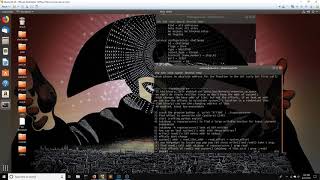
To help support me, check out Kite! Kite is a coding assistant that helps you faster, on any IDE offer smart completions and ... Our most complex topic yet - how to do ROPs with Okay so we're today we're going to cover return oriented programming for When modern security protections like Data Execution Prevention (DEP) or the NX bit stop you from executing shellcode on the ... Solving 'teufel' - pwnable 200 from the 32c3ctf. I didn't solve it during the CTF but worked through several writeups and doing ... Snyk loves CTF challenges just like this for
PS, jump into the HackTheBox Cyber Apocalypse CTF! Help the channel grow with a ... The Intel vPro® platform helps mitigate low-level In this video walk-through, we covered another scenario of The ropasaurusrex CTF from PLAIDCTF 2013, apologies for any incorrect explanations, please correct me in the comments. CTF Writeup Video 00:00 Intro 00:46 Running the Video walkthrough/tutorial for ROPEmporium challenge 7 - 'ret2csu' (64 bit). We're back in ret2win territory, but this time with no ...