Media Summary: Security+ Training Course Index: Professor Messer's Course Notes: ... CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... In this video I have explained the basics of #
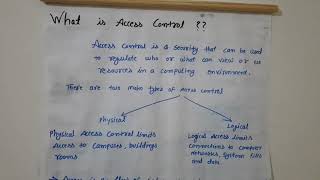
Access Controls Concepts - Detailed Analysis & Overview
Security+ Training Course Index: Professor Messer's Course Notes: ... CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... In this video I have explained the basics of # In this session, we break down one of the most critical topics in cybersecurity — This video is part of the computer/information/cyber security and ethical hacking lecture series; by Z. Cliffe Schreuders at Leeds ... IBM Security QRadar EDR : IBM Security X-Force Threat Intelligence Index 2023:
Role-based access control (RBAC) is an essential method for managing permissions in cloud systems. In this video, Varun sir ... Sections 0:00 Introduction 0:52 What is Authorization 1:47 Authorization Models 2:54 RBAC: Role-Based Hey everyone, In this video, we are going to see various role-based