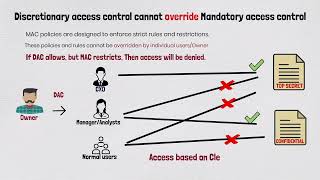
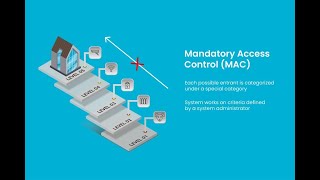
Media Summary: CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... The Biba Integrity Model provides two rules that help us think about the ways that we protect the integrity of data: the simple ...
Certmike Explains Mandatory Access Controls - Detailed Analysis & Overview
CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... The Biba Integrity Model provides two rules that help us think about the ways that we protect the integrity of data: the simple ... Get the threat intelligence guide → Learn about the technology → Exploring the ... In this session, we break down one of the most critical topics in cybersecurity — You can buy me a coffee if you want to support the channel: I
Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture introduces The Bell LaPadula Model is all about information confidentiality. The prevention of unauthorized DMARC, DKIM and SPF are three protocols that are widely used as enhanced security of email communications. The security that ... Developing a cybersecurity incident response plan is the best way to prepare for your organization's next possible cybersecurity ... Security+ Training Course Index: Professor Messer's Course Notes: ... Evaluating authentication systems are used to make sure that someone is who they claim to be before granting them
Subscribe here: CyberPlatter Discord ...