Media Summary: Tough, realistic CISSP Practice Tests designed to expose gaps before exam day. Don't go in unprepared.** Challenging ... If you don't understand the details of the (ISC)2 code of , you're giving up some easy points on your , , ... A business impact analysis identifies the business processes and tasks that are critical to an organization and the threats posed to ...
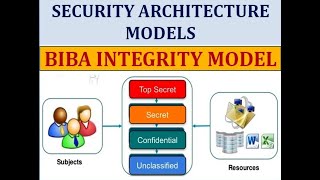
Certmike Explains The Biba Integrity Model - Detailed Analysis & Overview
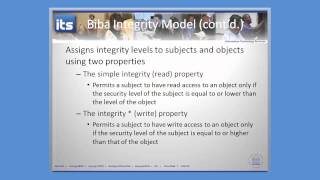
Tough, realistic CISSP Practice Tests designed to expose gaps before exam day. Don't go in unprepared.** Challenging ... If you don't understand the details of the (ISC)2 code of , you're giving up some easy points on your , , ... A business impact analysis identifies the business processes and tasks that are critical to an organization and the threats posed to ... here in this video I have compared Bell la phadula Developing a cybersecurity incident response plan is the best way to prepare for your organization's next possible cybersecurity ... In this video, we dive deep into the fascinating world of security
00:00 – Introduction 00:31 – What are Security Models? 01:48 – Bell–LaPadula Model 03:45 – Cryptography causes a lot of anxiety for candidates preparing for cybersecurity certification exams because it introduces an ... The NIST Cybersecurity Framework was published with the goal of providing a common language for understanding, managing ... Digital signatures use cryptography to provide authentication,