Media Summary: You can buy me a coffee if you want to support the channel: I explain In this session, we break down one of the most critical topics in cybersecurity — Here's the one piece of advice that I would have for someone who is looking to break into cyber
30 Mandatory Access Control Information Security 5 Secure Systems Engineering - Detailed Analysis & Overview
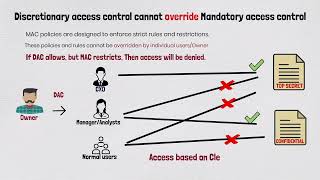
You can buy me a coffee if you want to support the channel: I explain In this session, we break down one of the most critical topics in cybersecurity — Here's the one piece of advice that I would have for someone who is looking to break into cyber Want To Know What Is DAC? This Video Explains The Concept Of Discretionary This video is part of the Udacity course "Intro to In today's cybersecurity world, controlling who has
Authentication vs Authorization identity verification, cybersecurity, authentication, authorization explained, ...