Media Summary: Get the threat intelligence guide → Learn about the technology → Exploring the ... In this session, we break down one of the most critical topics in cybersecurity — What is Access Control? 👇For more information, a link to the full video is given below. 👉What are ERT and ...
Basics Of Access Control - Detailed Analysis & Overview
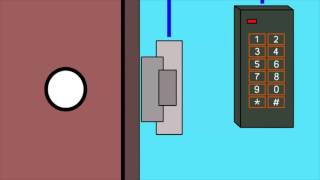
Get the threat intelligence guide → Learn about the technology → Exploring the ... In this session, we break down one of the most critical topics in cybersecurity — What is Access Control? 👇For more information, a link to the full video is given below. 👉What are ERT and ... CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... Have you ever wondered how secure doors work? Whether it's your office, home, or a high-security server room, What's going on everybody today we're building another
Network Security Course Lecture # 15 & 16 * Introduction to These are all questions that fall in the identity and - In this video, our expert technician will guide you through the ins and outs of Unlocking Secrets: A Simple Guide to Door