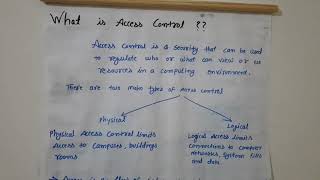
Media Summary: In this video I have explained the basics of # Get the threat intelligence guide → Learn about the technology → Exploring the ... What is Access Control? 👇For more information, a link to the full video is given below. 👉What are ERT and ...
Access Controls Cyber Security Lecture - Detailed Analysis & Overview
In this video I have explained the basics of # Get the threat intelligence guide → Learn about the technology → Exploring the ... What is Access Control? 👇For more information, a link to the full video is given below. 👉What are ERT and ... Security+ Training Course Index: Professor Messer's Course Notes: ... In this session, we break down one of the most critical topics in Role-based access control (RBAC) is an essential method for managing permissions in cloud systems. In this video, Varun sir ...
In this video, Faisal Nadeem shared 10 most important Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... This video is part of the computer/information/ Learn Basic Networking Concepts in just 1 minute! In this video, we break down the core fundamentals every IT professional, ...