Media Summary: Dive into the critical security aspects of JSON Web Tokens (JWTs) and uncover the most Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Learn the difference between session and token-based authentication on the web. Master Web Security in 12 weeks ...
What Are Common Jwt Vulnerabilities - Detailed Analysis & Overview
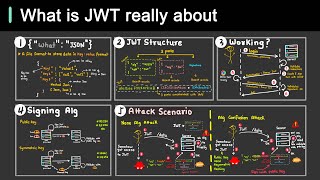
Dive into the critical security aspects of JSON Web Tokens (JWTs) and uncover the most Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Learn the difference between session and token-based authentication on the web. Master Web Security in 12 weeks ... LIKE and SUBSCRIBE with NOTIFICATIONS ON if you enjoyed the video! If you want to learn bug bounty hunting from me: ... In this video, we'll focus on the critical 'None' All my videos are for educational purposes with bug bounty hunters and penetration testers in mind YouTube don't take down my ...
In this comprehensive video, we dive deep into the security If you're hunting bugs and not checking for this Burp Suite Deep Dive course: In this video I demonstrate how you can Membership // Want to learn all about cyber-security and become an ethical hacker? Join this channel now to gain access into ... Key topics include: - JWT Basics & Architecture: A foundational overview of JSON Web Tokens. - Ace Your Interviews!** In this video, we dive into the **5