Media Summary: This playlist has a list of free videos from the course "Hacking and Securing JSON Web Tokens( In this video, we'll focus on the critical ' LIKE and SUBSCRIBE with NOTIFICATIONS ON if you enjoyed the video! If you want to learn bug bounty hunting from me: ...
Understanding Jwt Vulnerabilities The None Vulnerability - Detailed Analysis & Overview
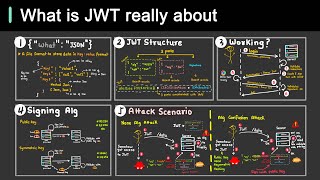
This playlist has a list of free videos from the course "Hacking and Securing JSON Web Tokens( In this video, we'll focus on the critical ' LIKE and SUBSCRIBE with NOTIFICATIONS ON if you enjoyed the video! If you want to learn bug bounty hunting from me: ... In this comprehensive guide, we delve into the world of JSON Web Tokens ( Welcome to our comprehensive tutorial about Dive into the critical security aspects of JSON Web Tokens (JWTs) and uncover the most common
JWT dikhta simple hai But agar implementation weak ho to attacker token forge karke admin ban sakta hai Aaj Day 117 me hum JWT ... Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: JSON Web Tokens, or JWTs, are handy little items commonly found in many web applications. They also have a few interesting ... Building secure multi-tenant SaaS platforms requires more than authentication alone. In this video, we explore 7 fundamental ... If you're hunting bugs and not checking for this