Media Summary: Welcome to a live TryHackMe session with Kyser Clark! This time, we're diving into the Web Application Pentesting Learning Path ... OAuth is a standard mechanism that we use every day. There are some Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter:
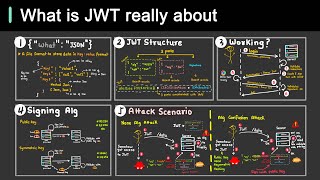
Jwt Security Vulnerabilities Cybersecuritytv - Detailed Analysis & Overview
Welcome to a live TryHackMe session with Kyser Clark! This time, we're diving into the Web Application Pentesting Learning Path ... OAuth is a standard mechanism that we use every day. There are some Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Support my work Here are a few tips on how to make your Membership // Want to learn all about cyber- JSON Web Tokens are powerful — but one wrong implementation can expose your entire application. In this video, we cover the ...