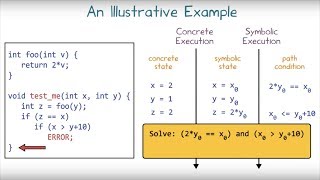
Media Summary: So today I'm gonna be talking about a I'll give you guys a little intro to Follow David on Twitter : Follow us on Twitter: at ... 📜w7 symbolic execution path constrained white box software testing
User Guided Symbolic Execution With Visualization - Detailed Analysis & Overview
So today I'm gonna be talking about a I'll give you guys a little intro to Follow David on Twitter : Follow us on Twitter: at ... 📜w7 symbolic execution path constrained white box software testing [CB23]Enhanced Vulnerability Hunting in WDM Drivers with MIT 6.858 Computer Systems Security, Fall 2014 View the complete course: Instructor: Armando ... Tuba Yavuz from University of Florida at the 3nd International KLEE Workshop on
The dual screen setup on Jannis' laptop was misbehaving. We've fixed the display of his slides and demo for the video. Rasool Maghareh from National University of Singapore at the 2nd International KLEE Workshop on





![[CB23]Enhanced Vulnerability Hunting in WDM Drivers with Symbolic Execution and Taint Analysis](https://i.ytimg.com/vi/nBOxWo_MC4M/mqdefault.jpg)