Media Summary: MIT 6.858 Computer Systems Security, Fall 2014 View the complete course: Instructor: Armando ... MIT 6.858: Computer Systems Security Lecture by Armando Solar-Lezama. Jingxuan He from ETH Zurich at the 3nd International KLEE Workshop on
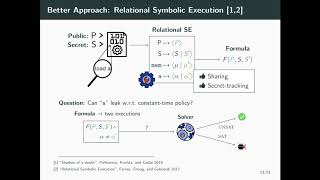
10 Symbolic Execution - Detailed Analysis & Overview
MIT 6.858 Computer Systems Security, Fall 2014 View the complete course: Instructor: Armando ... MIT 6.858: Computer Systems Security Lecture by Armando Solar-Lezama. Jingxuan He from ETH Zurich at the 3nd International KLEE Workshop on So today I'm gonna be talking about a I'll give you guys a little intro to How can static analysis tools detect bugs hidden deep inside complex code paths? In this Sonar Summit 2026 session, we ... A presentation by Benton Guess and Robert Dominguez for A&M's CSCE 451 Software Reverse Engineering taught by Dr. Liu.
Our engineering director Huck goes over how to use angr, a powerful tool to solve reverse engineering and binary exploitation ... More info at Get free access to all presentations and slides from FuzzCon Europe 2020 on: ... A lecture for BSc students in Innopolis University. Blog: Books: Following on from our look at z3 last Monday, today's talk will cover the basics of




![ECE 453/CS 447/CS 647 Winter 2023 [W05a] Symbolic Execution](https://i.ytimg.com/vi/kSj0Ssb77gY/mqdefault.jpg)











![PPA 8/10: Symbolic Execution [program analysis crash course]](https://i.ytimg.com/vi/PaCEIGcnx80/mqdefault.jpg)

