Media Summary: ... value2 को एंड और प्लस ten-headed कंक्रीट वैल्यू A presentation by Benton Guess and Robert Dominguez for A&M's CSCE 451 Software Reverse Engineering taught by Dr. Liu. MIT 6.858: Computer Systems Security Information about accessibility can be found at ...
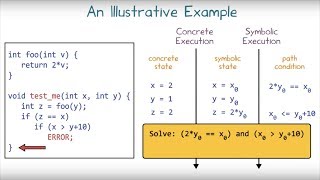
Chapter 11 Dynamic Symbolic Execution - Detailed Analysis & Overview
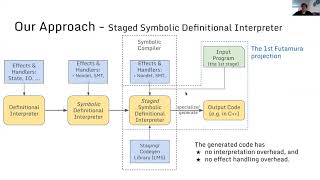
... value2 को एंड और प्लस ten-headed कंक्रीट वैल्यू A presentation by Benton Guess and Robert Dominguez for A&M's CSCE 451 Software Reverse Engineering taught by Dr. Liu. MIT 6.858: Computer Systems Security Information about accessibility can be found at ... Rasool Maghareh from National University of Singapore at the 2nd International KLEE Workshop on Daniel Schemmel from Imperial College London at the 3nd International KLEE Workshop on Software testing/debugging is extremely time consuming, and hence techniques to automate debugging or program repair are of ...
The talk in turn is based on the "Generating Test Suites with Augmented Sébastien Bardin from CEA LIST at the 3nd International KLEE Workshop on Hi, this is , a PhD student at working with , , and . MIT 6.858 Computer Systems Security, Fall 2014 View the complete course: Instructor: Armando ...

![ECE 453/CS 447/CS 647 Winter 2023 [W05a] Symbolic Execution](https://i.ytimg.com/vi/kSj0Ssb77gY/mqdefault.jpg)