Media Summary: Database security concerns the use of a broad range of information security Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... CyberPlatter Discord Channel: Website: Security Analyst and Engineer ...
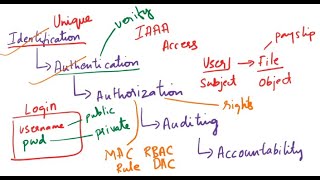
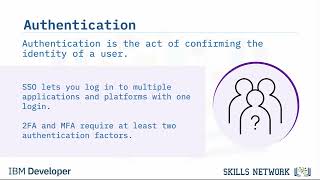
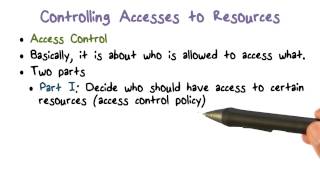
Unit 8 Lecture 1 Authentication Authorization And Access Control - Detailed Analysis & Overview
Database security concerns the use of a broad range of information security Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... ● 𝗗𝗕𝗠𝗦 𝗙𝘂𝗹𝗹 𝗖𝗼𝘂𝗿𝘀𝗲 👇 ● 𝗢𝗿𝗮𝗰𝗹𝗲 ... In this video Privacy & Security topic of operating Security+ Training Course Index: Professor Messer's Course Notes: ...
Welcome back to your Data Security Foundations Thanks For Watching--------------------------- Subscribe Kali Linux Hacker If You want to pass CEH exam subscribe us. This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... Get the threat intelligence guide → Learn about the technology → Exploring the ...