Media Summary: CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... IBM Security QRadar EDR : IBM Security X-Force Threat Intelligence Index 2023: Security+ Training Course Index: Professor Messer's Course Notes: ...
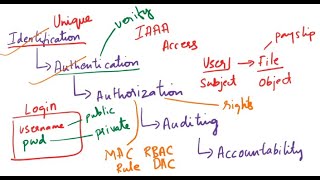
Cybersecurity Basics 8 Authentication Authorization - Detailed Analysis & Overview
CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... IBM Security QRadar EDR : IBM Security X-Force Threat Intelligence Index 2023: Security+ Training Course Index: Professor Messer's Course Notes: ... Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Animation ... In this video, Faisal Nadeem shared 10 most important Become a senior software engineer with a job guarantee:
Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... Here's the one piece of advice that I would have for someone who is looking to break into IBM Security QRadar EDR : Full Playlist: ...