Media Summary: Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... Security+ Training Course Index: Professor Messer's Course Notes: ... Get the threat intelligence guide → Learn about the technology → Exploring the ...
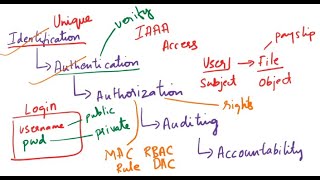
Cyber Security Access Control Authentication Authorization - Detailed Analysis & Overview
Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... Security+ Training Course Index: Professor Messer's Course Notes: ... Get the threat intelligence guide → Learn about the technology → Exploring the ... In this session, we break down one of the most critical topics in In this video I have explained the basics of # This video consists of easy to understand introductions to IAM (Identity and
In this video, We have covered basic to identification,