Media Summary: This playlist/video has been uploaded for Marketing purposes and contains only selective videos. For the entire video course and ... This video tutorial has been taken from Hands-On Penetration Testing with This video tutorial has been taken from Beginning
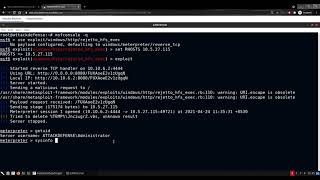
Mastering Metasploit 5 0 Post Exploitation Process Packtpub Com - Detailed Analysis & Overview
This playlist/video has been uploaded for Marketing purposes and contains only selective videos. For the entire video course and ... This video tutorial has been taken from Hands-On Penetration Testing with This video tutorial has been taken from Beginning Ethical Hacking with Metasploitable2 (Part 2) Welcome to Part 2 of our Ethical Hacking with Metasploitable2 series! This video tutorial has been taken from Learning DISCLAIMER All our videos are for EDUCATIONAL PURPOSES ONLY. Don't une them for illegal activities. You are the only ...
Room link: MISSION BRIEFING Aboard the long-haul vessel EPOCH-1, the MedBay ... See how the FakeLogonScreen utility is used to create a fake Windows user logon screen on the target machine, which allows an ... This video tutorial has been taken from Practical Windows Penetration Testing. You can learn more and buy the full video course ...