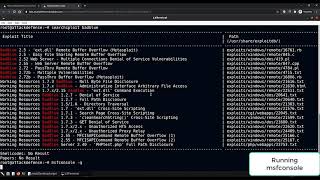
Media Summary: In this video, I cover the process of establishing An insecure application is running on the target machine, which is vulnerable to Buffer Overflow. In this lab, you would learn about ... Try This On a Virtual machine Straight Warning Do Not Try This On a Real PC.
Windows Post Exploitation Persistence With Metasploit - Detailed Analysis & Overview
In this video, I cover the process of establishing An insecure application is running on the target machine, which is vulnerable to Buffer Overflow. In this lab, you would learn about ... Try This On a Virtual machine Straight Warning Do Not Try This On a Real PC. Receive video documentation ---- Do you need private ... The primary aim of this video is to explore the utilization of Hi there! New to Ethical Hacking? If so, here's what you need to know -- I like to share information a LOT, so I use this channel to ...
Subscribe our You Tube channel and visit : In this video we look at maintaining access to a Making Of Persistent Backdoor (Metasploit - Kali Linux) Exploitation and Persistence with Metasploit, Powershell and WMI Take a deep dive into Meterpreter, and see how in-memory payloads can be used for Creating a persistent reverse shell with Metasploit
Learn to use the espia Meterpreter exention and capture target machine's screenshot using Screengrab and Meterpreter ...








![[PRACTICAL]Using Metasploit Framework For Post-Exploitation And Cleaning Up[HINDI]](https://i.ytimg.com/vi/1mWga5uWv28/mqdefault.jpg)








