Media Summary: The primary aim of this video is to explore the utilization of In this video, I cover the process of establishing persistence on Hello friends in this video, I show you how to use
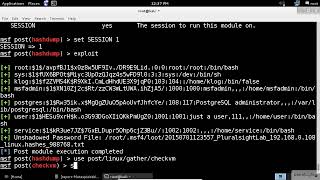
Metasploit Post Modules On Windows System Exploit Post Exploitation - Detailed Analysis & Overview
The primary aim of this video is to explore the utilization of In this video, I cover the process of establishing persistence on Hello friends in this video, I show you how to use Hak5 -- Cyber Security Education, Inspiration, News & Community since 2005: Join Rob Fuller on this ethical hacking ... Here we gain access through a previous brute force, gain a PortScanning Pivoting With Metasploit Post Exploitation
In this video we go over some of the benefits we get from a In this tutorial will go step-by-step through Video from Derbycon 2012. All videos, with downloads, can be found at this link shortly: ... A comprehensive step by step beginner's guide to Learn






![Windows Post Modules - Metasploit Minute [Cyber Security Education]](https://i.ytimg.com/vi/kGqPS7a3Tco/mqdefault.jpg)