Media Summary: This playlist/video has been uploaded for Marketing purposes and contains only selective videos. For the entire video course and ... Thank you for watching this video! Suggestions and Feedback: Join my discord server: ... This video tutorial has been taken from Hands-On
Practical Windows Penetration Testing About Post Exploitation Packtpub Com - Detailed Analysis & Overview
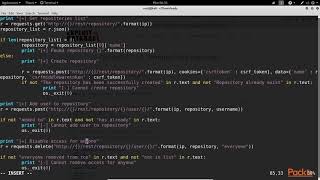
This playlist/video has been uploaded for Marketing purposes and contains only selective videos. For the entire video course and ... Thank you for watching this video! Suggestions and Feedback: Join my discord server: ... This video tutorial has been taken from Hands-On Membership // Want to learn all about cyber-security and become an ethical hacker? Join this channel now to gain access into ... Hak5 -- Cyber Security Education, Inspiration, News & Community since 2005: Join Rob Fuller for Learn how to pivot the target network using Meterpreter Part of Expert Metasploit
Hi there! New to Ethical Hacking? If so, here's what you need to know -- I like to share information a LOT, so I use this channel to ... In this video, I cover the process of establishing persistence on In this lab, pivot to the second machine and forward its port to gather information and WELCOME TO GREY WORLD GUYS Today I'm Going TO Show You What is a





![The 3 (or 4) P's of Post Exploitation - Practical Exploitation [Cyber Security Education]](https://i.ytimg.com/vi/OcEKXyJ8oqs/mqdefault.jpg)

![[PRACTICAL]Manual Post-Exploitation And Cleaning Up[HINDI]](https://i.ytimg.com/vi/soVK6nHvoI0/mqdefault.jpg)







