Media Summary: Hi, In series of recent campaigns, Adversaries started using Microsoft One Note Center I wrote a blog post about analyzing In which we use static and dynamic techniques to review the goofiest delivery mechanism ever. 0:00 Preroll 9:57 Intro 15:36 ...
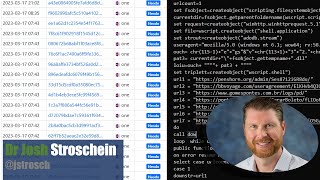
Malicious Onenote Documents Malware Analysis - Detailed Analysis & Overview
Hi, In series of recent campaigns, Adversaries started using Microsoft One Note Center I wrote a blog post about analyzing In which we use static and dynamic techniques to review the goofiest delivery mechanism ever. 0:00 Preroll 9:57 Intro 15:36 ... You can buy me a coffee if you want to support the channel: I explain and demonstrate the ... In this full series we will talk about Incident Response and it will be a Free Training Course for everyone. Today is Day-15 and I ... Stay protected from the latest cyber threat with this breaking news video about the "QakNote"