Media Summary: Hi, In series of recent campaigns, Adversaries started using Microsoft One Note documents for In which we use static and dynamic techniques to review the goofiest delivery mechanism ever. 0:00 Preroll 9:57 Intro 15:36 ... You can buy me a coffee if you want to support the channel: I explain and demonstrate the ...
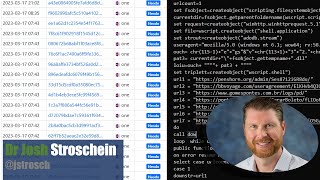
Blitz 45 Seconds Onenote Malware Analysis - Detailed Analysis & Overview
Hi, In series of recent campaigns, Adversaries started using Microsoft One Note documents for In which we use static and dynamic techniques to review the goofiest delivery mechanism ever. 0:00 Preroll 9:57 Intro 15:36 ... You can buy me a coffee if you want to support the channel: I explain and demonstrate the ... Tackling another Lets Defend Challenge, that being the "QakBot Every month, our experts Nick, Hugh and Arron will highlight the current and emerging cyber threats you need to know about right ...