Media Summary: Hi, In series of recent campaigns, Adversaries started using Microsoft One Note You can buy me a coffee if you want to support the channel: I explain and demonstrate the ... Stay protected from the latest cyber threat with this breaking news video about the "QakNote"
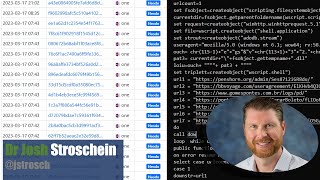
Analyzing Malicious Onenote Documents - Detailed Analysis & Overview
Hi, In series of recent campaigns, Adversaries started using Microsoft One Note You can buy me a coffee if you want to support the channel: I explain and demonstrate the ... Stay protected from the latest cyber threat with this breaking news video about the "QakNote" Source: Ever since Microsoft blocked macros by default in Office applications, ... Keeper Security offers a privileged access management solution to deliver enterprise grade protection all in ... In which we use static and dynamic techniques to review the goofiest delivery mechanism ever. 0:00 Preroll 9:57 Intro 15:36 ...
In what's looking like a new trend for 2023, we're seeing a sharp increase in phishing attacks that are using new and ...