Media Summary: In case you didn't have time for our 2-minutes introduction to the topic ( :) More information at: ... Read our blog post about Attachments in Phishing In this video we introduce the formula view, which is extremely useful when
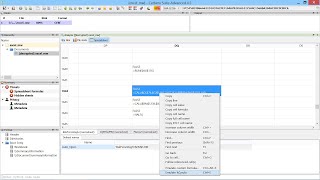
Malicious Excel Document Analysis In Cerbero Suite - Detailed Analysis & Overview
In case you didn't have time for our 2-minutes introduction to the topic ( :) More information at: ... Read our blog post about Attachments in Phishing In this video we introduce the formula view, which is extremely useful when You can find the script used in the video on our blog: https:// The first of the short instructional videos that we're currently producing. If you like the idea, make sure to like the video! Check out ...