Media Summary: How to quickly inspect a malicious PDF and extract its shellcode. If you're interested in a complete The first of the short instructional videos that we're currently producing. If you like the idea, make sure to like the video! Check out ... This video answers Frequently Asked Questions related to
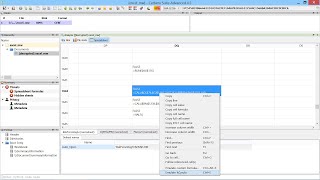
File Analysis Using Cerbero Suite - Detailed Analysis & Overview
How to quickly inspect a malicious PDF and extract its shellcode. If you're interested in a complete The first of the short instructional videos that we're currently producing. If you like the idea, make sure to like the video! Check out ... This video answers Frequently Asked Questions related to This video is the extract from the E-SPIN monthly webinar event entitled Since lately I've been playing some CTFs to test new features in Filters are a great way to simplify tasks you might encounter every day. If you haven't yet
Presentation of our HybridAnalysis Intelligence commercial package for Hopefully a comprehensible introduction of how to A brief introduction on how to inspect Windows crash dumps in We have uploaded a version of the same video