Media Summary: In this workshop (2 hours), I explain how to use the tools (oledump, emldump, YARA rules, …) I developed to In case you didn't have time for our 2-minutes introduction to the topic ( :) More information at: ... Today we tackle the new exercises in Lets Defend, these are
Malicious Office Document Dde Analysis In 30 Seconds - Detailed Analysis & Overview
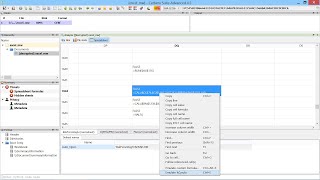
In this workshop (2 hours), I explain how to use the tools (oledump, emldump, YARA rules, …) I developed to In case you didn't have time for our 2-minutes introduction to the topic ( :) More information at: ... Today we tackle the new exercises in Lets Defend, these are 0:00 Intro 0:17 Course content 0:45 Why should we worry about Microsoft Ring Ø Labs: How do you get started in # 0:00 Intro 2:00 olemeta 4:02 oleid 6:50 olevba You can access this course on LetsDefend for doing practice online: ...
Did you know that you could infect your computer just by opening a pdf or Microsoft