Media Summary: Share part of a secret without knowing which part? Dr Tim Muller explains how Paper by Alex Grilo, Huijia Lin, Fang Song, Vinod Vaikuntanathan presented at Eurocrypt 2021 See ... This video is part of an online course, Applied Cryptography. Check out the course here:
Lecture 20 Secure Computation And Oblivious Transfer - Detailed Analysis & Overview
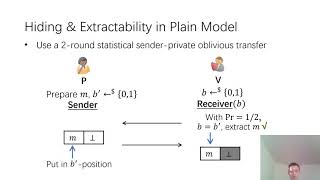
Share part of a secret without knowing which part? Dr Tim Muller explains how Paper by Alex Grilo, Huijia Lin, Fang Song, Vinod Vaikuntanathan presented at Eurocrypt 2021 See ... This video is part of an online course, Applied Cryptography. Check out the course here: [Link to slides below] In this Invisible Garde session (hosted by the PSE heading towards DevConnect Buenos Aires) the general ... Paper by Vipul Goyal, Abhishek Jain, Zhengzhong Jin, Giulio Malavolta presented at Eurocrypt 2020 See ... Spring 2018 Cryptography & Cryptanalysis Prof. Vinod Vaikuntanathan.
This educational video is part of the course Quantum Cryptography available for free via http:/www.online-learning.tudelft.nl ... Paper by Arka Rai Choudhuri, Michele Ciampi, Vipul Goyal, Abhishek Jain, Rafail Ostrovsky presented at TCC 2021 See ... Authors: Marcel Keller, Emmanuela Orsini and Peter Scholl (University of Bristol) presented at CCS 2016 - the 23rd ACM ...